The Importance of Regular Website Maintenance
Introduction
How are you? As the owner of a website, I know how important it is to have a web presence that shows off your brand and keeps people interested. But it’s not enough to just have a website. To keep it working well and smoothly, it needs to be taken care of regularly. If you don’t keep up with website maintenance, it can lead to security holes, slow performance, and content that is out of date. That’s why I’m excited to tell you why website maintenance is so important and how a local developer can help.
In this blog post, I’ll talk about why website maintenance is important, list some common maintenance tasks, and talk about why it’s a good idea to hire a local developer to help with website maintenance. So, let’s dive in!
How Important it is to keep up a website
A website’s long-term success depends on how well it is kept up. A website is a representation of your brand or business, and it’s often the first time a potential customer meets you. If your website is old, slow, or full of mistakes, it can give visitors a bad impression and cause you to lose potential customers.
The security of your website is one of the most important reasons to keep it up to date. With the number of cyber threats growing, it’s important to make sure your website is safe and has the latest security patches. Hackers can take advantage of security holes in old software, which can lead to data leaks, malware infections, and other problems that can hurt your business and reputation.
Another reason to keep up with your website is to make sure it works well. When a website is slow, visitors can get frustrated and leave, which makes the bounce rate go up and leads to a drop in traffic and sales. Maintaining your website regularly can help improve its performance, which can lead to faster load times, a better user experience, and a higher ranking in search engines.
Why You Should Hire A Local Developer

Hiring a local developer to keep up with your website can help your business in a number of ways. Here are a few reasons why it’s good to work with a local developer:
Expertise in maintaining websites:
A local developer has experience and knowledge in maintaining websites. They have the skills and knowledge to do regular maintenance tasks like software updates, backups, and security checks. This keeps your website running smoothly and safely.
Customization and personalization:
If you work with a local developer, you can get solutions that are made to fit the needs of your business. They can help you find places where your website could be better and put in place personalised solutions that will improve your website’s performance, user experience, and ability to do what it’s supposed to do.
Communication and access:
When you work with a local developer, you can talk directly to the person who is in charge of keeping your website up-to-date. This lets you get updates on a regular basis and quick answers to any questions or worries you may have. Also, a local developer is easy to meet with in person, which makes it easier to talk about complicated issues and give feedback.
Quick response time:
A local developer can fix problems with your website quickly, which cuts down on downtime and reduces the impact on your business. They can also help you out in an emergency and fix important problems quickly, making sure that your website is up and running as soon as possible.
Why your website needs to be updated often
Maintenance is important if you want your website to work well, be secure, and be easy to use. Here are some reasons why you need to keep up with maintenance on your website:
Security patches and updates:
As part of regular maintenance, you should apply security patches and updates to the software and plugins on your website. When software is out of date, it can leave holes that hackers can use to steal sensitive data, install malware, or do other bad things. Keeping your website up-to-date helps keep it safe and stops possible security breaches.
Performance optimization:
Taking care of your website means optimizing its performance so that it loads quickly and gives users a good experience. This includes things like caching, optimizing the database, and making images as small as possible. If your website is slow, visitors may get frustrated and leave, which can hurt your search engine rankings and online visibility.
Content management:
Part of regular maintenance is making sure that your website’s content is correct, up-to-date, and relevant. This can mean making new pages, updating information about products, or putting up blog posts. Fresh, interesting content can bring people to your website, keep them there, and help it rank higher in search engines.

Improvements to the user experience:
Regular maintenance also includes improvements to the user experience, such as fixing broken links, making the site easier to navigate, and making sure it works well on mobile devices. A website that is easy to use can get people more interested and keep them on your site longer, which can lead to more sales and more money.
Updates to security:
Security updates are an important part of maintaining a website. They are very important if you want to keep your website safe from cyber-attacks and data leaks. Developers of software often put out security updates to fix known bugs and close security holes in their programs.
If you don’t apply these updates as soon as they come out, your website could be vulnerable to hacking attempts, malware infections, and data theft.
When a security hole is found, it can get a lot of attention, which hackers can use to attack vulnerable websites. Because of this, it’s important to get security updates as soon as possible so that your website doesn’t become a target.
Cybercriminals can sometimes use automated tools to look for websites that haven’t updated their security. This makes it easier for them to target vulnerable sites.
Also, software and plugins that are too old can cause problems with compatibility and make a website stop working or give errors. These problems can cause downtime and hurt the usability, user experience, and search engine rankings of your website. By installing security updates, you can prevent these compatibility problems and make sure that your website works and works well.
To keep your website safe, you need to work with a local developer or a reputable website maintenance service that can do regular security updates and patches. They can make sure that all of your website’s software and plugins are up-to-date, which lowers the risk of security holes and data breaches.
In short, it’s important to install security updates to keep your website safe and running well. If you don’t install these updates, your website could be open to cyber threats, data breaches, and other problems. By investing in regular website maintenance that includes security updates, you can reduce the risk of security holes, protect your business and reputation, and give your visitors a safe and interesting online experience.
Optimization of performance
Performance optimization is an important part of maintaining a website. It includes many tasks that can help your website run faster, be easier to use, and work better overall.
Here are some ways to improve your website’s performance that your local developer can use:
Caching:
Caching is the process of storing website data, like images and HTML files, that are often viewed in temporary storage or memory. This can help speed up the time it takes for your website to load and make it work better.
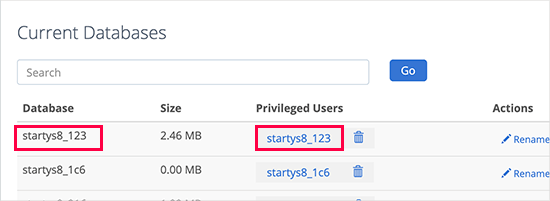
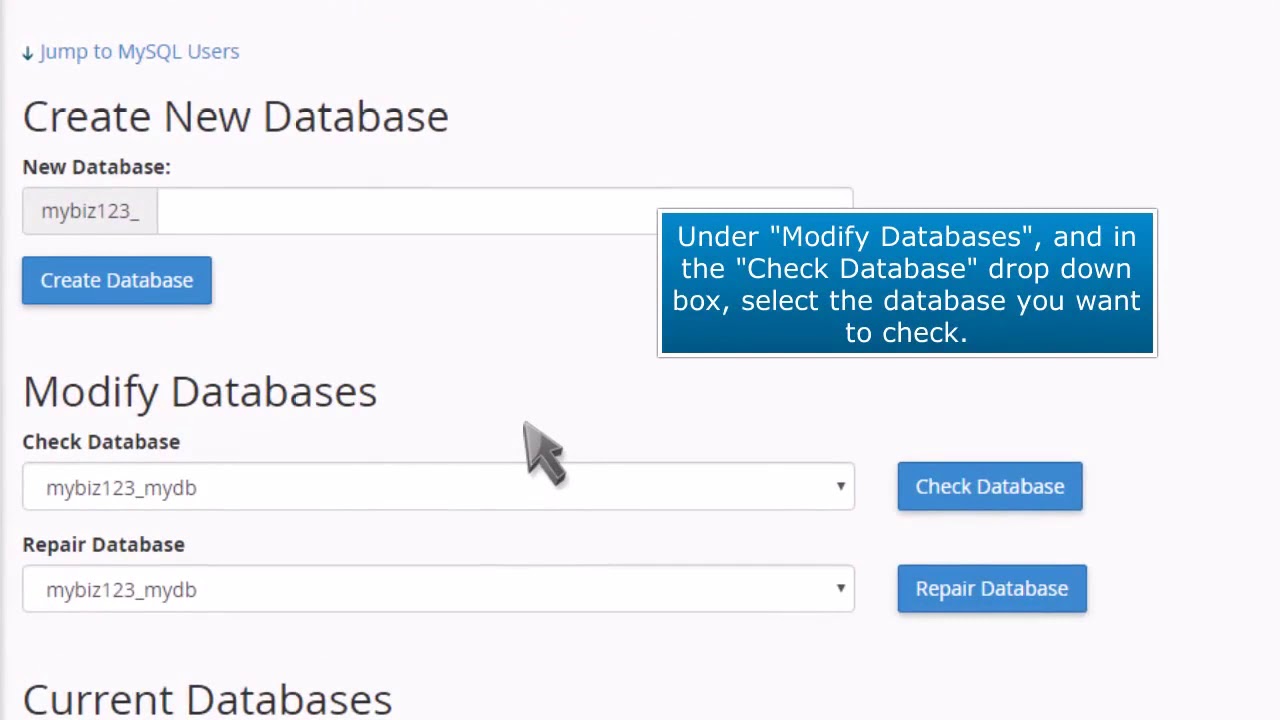
Database optimization:
If your databases get too big or aren’t set up well, they can slow down the speed of your website. By getting rid of unnecessary data and making the database structure better, optimizing your database can help your website run faster and work better.
Large image files can slow down the time it takes for your website to load. Your local developer can improve the performance of your website by compressing your images without hurting their quality. This will reduce the file size and speed up your website.
Content Delivery Network (CDN):
A CDN is a network of servers that can help get your website’s content to visitors faster. A content delivery network (CDN) can be set up for your website by a local developer. This can cut down on the distance and time it takes for people to access your website’s content, making your website faster and better.
Minimizing HTTP requests:
Getting your website to make fewer HTTP requests can help it load faster. Your local developer can improve the code on your website by getting rid of code that isn’t needed, compressing files, and combining multiple requests into one.
By using these performance optimisation techniques, your website will load faster and be easier to use for your visitors. A faster website can make people more interested, keep them on it longer, and help it rank higher in search engines. Improving the performance of your website can also lower the number of people who leave your site without staying and increase the number of people who stay on your site. This can lead to more sales or leads for your business.
Content management
Content management is an important part of keeping a website running. It means keeping the content on your website up-to-date and making sure it’s still useful, accurate, and interesting for your audience. Here are some ways in which your local developer can help you manage content:
Content creation: Your local developer can help you make high-quality content that is optimised for search engines and tailored to your target audience. They can help you write blog posts, product descriptions, and other website content that is interesting, informative, and relevant to your business.
Content updates:
It’s important to keep your website’s content fresh and up-to-date by changing it often. Your local developer can help you add new content, images, and videos to your website. This will keep your website fresh and interesting for your audience.
Content optimization:
Your local developer can help you make sure that the content on your website is optimized for search engines so that it can be seen by the people you want to see it. This means making sure that your website’s titles, descriptions, and meta tags are as good as they can be so that it show up higher on search engine results pages.
In short, content management is an important part of keeping a website running. By working with a local developer to manage the content on your website, you can make sure it stays up-to-date, accurate, and interesting for your visitors. By updating and optimising your website’s content on a regular basis, you can boost its visibility, search engine rankings, and overall performance, which can help your business do better online.
User experience improvements
User experience (UX) is an important part of maintaining a website. UX refers to how people interact with your website and how they feel as a whole while they’re using it. Here are some ways that your local developer can help improve your website’s user experience:
Responsive design:
Since more and more people are accessing websites on their phones, it is important to have a responsive design to make sure that your website is easy to use and accessible on all devices. Your local developer can help you make a design that works on different screen sizes and devices. This will make sure that everyone who visits your website will find it easy to use.
Navigation is an important part of the user experience. Your local developer can help you make a navigation menu that is clear and easy to use. This will make it easy for people to find the information they want on your website.
Page load speed:
If a page takes too long to load, it can ruin the user experience and make people leave your website. Your local developer can help you optimise the speed at which pages load on your website. This will make sure that your website loads quickly and efficiently.
Accessibility:
It’s important for a good user experience to make sure that your website is accessible to all visitors, including those with disabilities. Your local developer can help you make sure that your website is accessible by adding things like alt tags for images, captions for videos, and keyboard navigation.
By making your website’s user experience better, you can get more people to stay on it, reduce the number of people who leave right away, and improve your website’s overall performance. A good user experience can also lead to more conversions and sales, which can help your business have a more successful online presence.
Typical maintenance jobs
It’s important to do regular maintenance on your website to keep it working, secure, and up-to-date. Here are some common maintenance tasks that your local developer can do to keep your website running smoothly:
Security updates:
Your local developer can make sure that your website’s security software is up to date, which protects your website from potential threats and holes.
Software updates:
Updating your website’s software, like your content management system (CMS) and plugins, on a regular basis can make sure that your website is using the most recent and safest version.
Backups:
It’s important to back up your website’s data on a regular basis so that you have a copy of the content and information in case your website crashes or you lose data.
Broken links and mistakes:
Your local developer can check for and fix any broken links or mistakes on your website on a regular basis, making sure that visitors can use your site without any trouble.
Performance optimization:
Improving your website’s performance, such as the speed at which pages load and the speed at which the whole site runs, can make the user experience better and help your site rank higher in search engine results in pages.
Content updates:
Adding and changing your website’s content on a regular basis can help keep it fresh, relevant, and interesting for visitors.
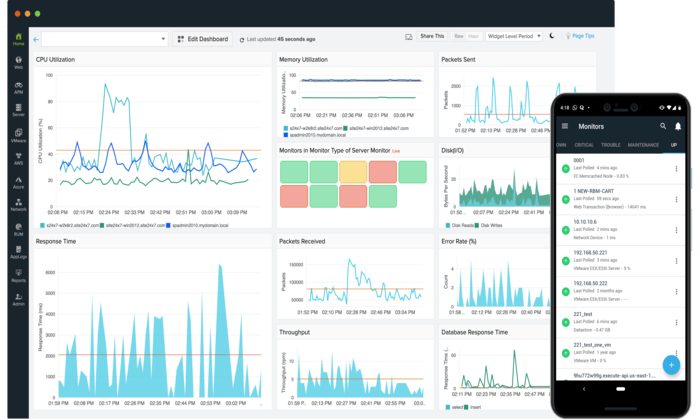
Analytics and tracking:
Looking at your website’s traffic and how people use it can give you valuable information about how people use your site. This lets you make decisions based on data to improve your website’s performance and user experience.
Your local developer can help keep your website safe, up-to-date, and easy to use by taking care of these common maintenance tasks. Regular maintenance can also help you avoid problems and save you time and money in the long run by letting you fix problems as soon as they show up.
Backups and contingency plans
Website maintenance isn’t complete without backups and plans for dealing with disasters. Having a backup can help you quickly get your website back to the way it was before a crash, data loss, or security breach.
Here are some important things that your local developer can help you with when it comes to backups and disaster recovery:
Regular backups:
Your local developer can help you set up and schedule regular backups of the files, databases, and other important information on your website. By making regular backups, you can make sure you have a complete and up-to-date copy of your website’s data in case something goes wrong.
Offsite backups:
Storing your backups away from your website can help protect its data in case of a natural disaster, like a fire or flood. Your local developer can help you set up and configure offsite backups to make sure the data on your website is safe and secure.
Testing your backups:
Testing your backups regularly can help you make sure they are working correctly and that you can quickly and easily restore your website in case of an emergency. Your local developer can help you test your backups and make any improvements or changes that are needed.
Plan for dealing with disasters:
If you have a plan for dealing with disasters, you can respond quickly and effectively to things like a website crash, data loss, or security breach. Your local developer can help you make a disaster recovery plan that tells you what to do in case of a disaster and what each member of your team is responsible for.
Security concerns: Backups can also be attacked by ransomware or other security threats. Your local developer can help you set up security measures like encryption, access controls, and malware scanning to keep your backups safe.
By working with a local developer to set up backups and disaster recovery, you can help protect the data on your website and make sure you can get back up and running quickly if something goes wrong. Regular backups and testing, storage off-site, and a well-thought-out disaster recovery plan can help keep your website up and running and lessen the damage from a disaster.
Updates to plug-ins and software
Updating your website’s plugins and software regularly is important for keeping your website safe, fast, and useful.
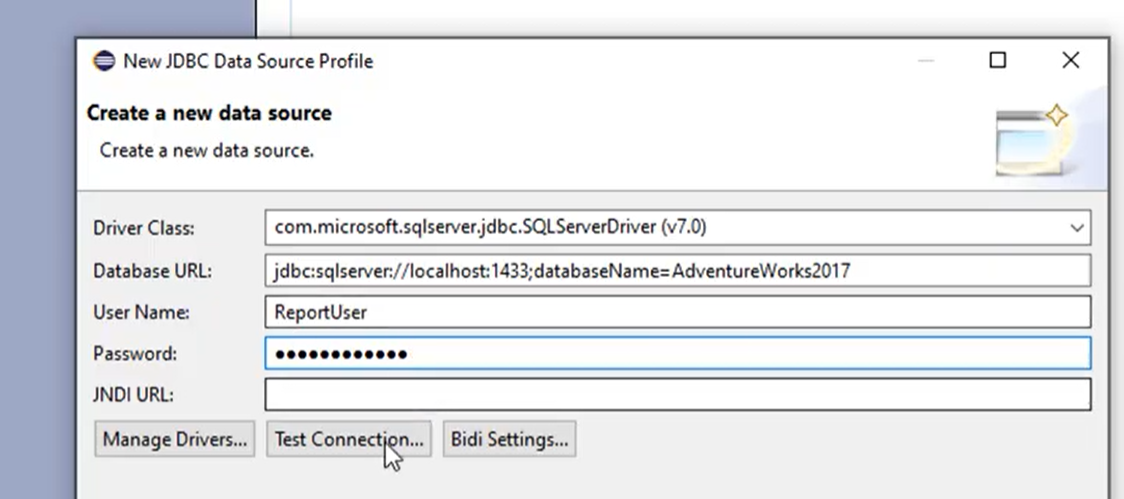
Here are some important things that your local developer can help you with when it comes to updating plugins and software:
Security updates: Updates usually include security patches that fix flaws or weaknesses that hackers could use to get into your website. Your local developer can help you make sure that the software and plugins on your website are up-to-date with the latest security patches.
Performance improvements: Updates can also improve the speed and responsiveness of your website by making changes to how it works. Your local developer can help your website run better by updating your software and plugins regularly.
Compatibility issues: Older versions of plugins and software may not work with the latest versions of your website’s CMS or other software. Your local developer can help make sure that your website’s plugins and software work with the latest versions of your CMS and other software.
Fixes for bugs: Updates can also include fixes for bugs that fix problems or glitches that could affect how well your website works. Your local developer can help make sure that the software and plugins on your website are up-to-date and have the latest bug fixes.
New features: Updates can also add new features and functions that can improve how users interact with and use your website. You can use these new features and add them to your website with the help of a local developer.
Testing:
Before updating the plugins and software on your website, your local developer can help you test them in a staging environment to make sure they don’t cause any problems with how your website works.
By updating your website’s plugins and software regularly, you can help make sure that it stays safe, works well, and gives users a good experience. Your local developer can help you keep up with the latest updates, patches, and bug fixes. They can also help you test and integrate new features and functions.
Increasing the speed of a site
Site speed optimisation is an important part of website maintenance that can have a big effect on how well your site works and how users feel about using it. Here are some important ways in which your local developer can help you speed up your site:
Image optimisation:
Images are often one of the biggest files on a website, which can make it take a lot longer for your website to load. Your local developer can help you optimise your website’s images by compressing them and reducing their file sizes without sacrificing quality.
Minification of code: When you “minify” the code on your website, you get rid of characters, white space, and comments that aren’t needed. This helps reduce the file size of the code and makes your website load faster. The HTML, CSS, and JavaScript code on your website can be made smaller with the help of a local developer.
Caching:
Caching is the process of storing data that is often used, like images and code, in a user’s browser or on a server to make it faster to load a page. Your local developer can help you set up your website’s caching settings to make it load faster.
Content Delivery Network (CDN):
A CDN is a network of servers that are spread out all over the world and can help shorten the distance between your website’s server and a user’s browser. Your local developer can help you add a CDN to your website so that people all over the world can load it faster.
Server optimization: The speed at which your website loads can also be affected by how well your server works. Your local developer can help you optimize your website’s server settings, like the time it takes for the server to respond, to make it load faster.
Testing: Your local developer can do speed tests before and after making changes to your website to make it load faster. This lets them see how much the speed has improved and if any other areas need to be optimized.
By making your website load faster, you can improve the user experience, lower the number of people who leave right away, and get more people to buy from you. To make your website load faster and work better, your local developer can help you with image optimization, code minification, caching, CDN integration, server optimization, and testing.
Broken link and error checks
Broken links and other mistakes can make it hard for people to use your website and hurt its search engine ranking. Checking for broken links and errors on your website on a regular basis is an important part of maintenance that your local developer can help you with.
Here are a few important things to know about broken link and error checks:
Broken links:
Links on your website that no longer work because the page they lead to has been taken down or because the URL has changed. Broken links can make the user experience bad and make visitors angry. Your local developer can help you figure out which links on your website are broken and fix them.
404 errors:
A user gets a 404 error when they try to go to a page on your website that doesn’t exist anymore. This can happen when a link is broken or when a page is moved or renamed without the right redirects. You can find and fix 404 errors on your website with the help of a local developer.
Form validation:
Forms on your website, like contact forms or registration forms, may have mistakes that make it impossible for users to send them. Your local developer can help you set up form validation so that users can fill out and send forms without getting errors.
Site-wide error checks: Your local developer can do regular site-wide error checks to find and fix any other errors or problems that might be affecting how your website works or how users feel about it.
By regularly checking your website for broken links and other mistakes, you can make it easier for people to use and boost its search engine ranking. Your local developer can help you find and fix broken links, 404 errors, form validation problems, and other mistakes that could be slowing down your website.
Mobile responsiveness testing
In the mobile-first world of today, it’s important for websites to be mobile-friendly. Mobile responsiveness testing is an important part of website maintenance that can be done with the help of a local developer. Here are some important parts of testing for mobile responsiveness:
Compatibility with devices: There are a lot of different mobile devices with different screen sizes, resolutions, and operating systems. Your local developer can help you test how well your website works on different mobile devices to make sure it looks good on all of them.
Design that works well on mobile devices: The layout of your website should change automatically to fit different screen sizes and orientations. Your local developer can help you implement responsive design principles to ensure that your website is mobile-friendly.
Navigation and user experience:
When it comes to a website’s navigation and user experience, mobile users have different needs. Your local developer can help you test and improve your website’s navigation and user experience for mobile users, such as where buttons, fonts, and images are placed and how big they are.
Page speed:
Mobile users expect pages to load quickly, and pages that take too long to load can cause a lot of people to leave. Your local developer can help you test and improve the page speed of your website for mobile users, such as by compressing images and reducing the amount of code.
Google’s mobile-first indexing means that it mostly looks at the mobile version of a website’s content when it comes to indexing and ranking it. Your local developer can help you make sure that your website is optimised for mobile-first indexing, such as by using structured data and optimising for voice search.
Why hiring a local developer for website maintenance can be a good idea
There are many reasons to hire a local developer for website maintenance. Here are some key advantages:
Service that is tailored to your needs:
A local developer can give you service that is tailored to your needs. They can work with you closely to learn about your business and website goals and come up with solutions that fit your needs.
Quick response times:
If you need help or support with your website, a local developer can help you right away. They can fix any problems quickly and keep your site from going down as much as possible, so it’s always up and running.
Cost-effective:
Hiring a local developer to maintain a website can be cheaper than hiring a full-time employee or sending the work to a big agency. You can get the help you need for less money, and you only have to pay for the services you use.
Local knowledge:
A local developer knows a lot about the local market and can give you advice and tips that are right for your area. They can also help you improve the visibility of your website in local search results by giving you local SEO services.
Long-term relationship:
A local developer can work with you for a long time and help you with your website in the long run. They can help you come up with a full maintenance plan and keep your website running at its best with regular updates and optimisations.
Overall, hiring a local developer to maintain a website can give you personalised service, quick responses, low costs, local knowledge, and a long-term relationship. You can make sure your website is well-kept and set up for success by working closely with a local developer.
Knowledge of how to keep a website running
To keep your website up-to-date, secure, and running at its best, you need to know a lot about how to maintain it. Here are some of the most important areas of website maintenance that your local developer can help you with:
Technical knowledge: A local developer knows a lot about HTML, CSS, JavaScript, PHP, and other website technologies. They can fix technical problems, improve how well your website works, and make sure it meets current web standards.
Security: Your website and its visitors need to be safe from cyber threats, so website security is very important. To protect your website from attacks, your local developer can set up security measures like SSL certificates, firewalls, and malware scanning.
Managing your website’s content is important if you want to keep people interested and move up in the search engine rankings. Your local developer can help you update your content, add new pages, and make sure your content is SEO-friendly.
Search engine optimisation, or SEO, is very important if you want your website to show up higher on search engine results pages. Your local developer can help you with SEO by adjusting your website’s structure, content, and metadata to make it more visible to search engines.
Backup and disaster recovery: If you want to protect your website in case of an outage or data loss, you need to back it up often and have a plan for what to do in case of a disaster. Your local developer can set up backup and disaster recovery plans for your website to make sure it is always safe.
By hiring a local developer who knows how to maintain websites, you can make sure that your site is always up-to-date, safe, and running at its best. They can help with technical issues, security, content management, search engine optimisation, backup and disaster recovery, and more. With their help, you can keep up a website that keeps people interested, helps your search engine ranking, and helps you reach your business goals.
Customizing and making something unique
Customization and personalization are important parts of website maintenance that can help users have a better experience and become more involved. Here are some ways your local developer can help you customise and personalise:
Customized design: Your local web developer can make a website that is unique to your brand and business goals. They can make a design that is different from anything else on the market and gets the attention of your target audience.
Personalized user experience: Your local developer can change how people use your website by looking at how they use it and what they like. They can give each user recommendations, promotions, and content that appeals to them, which makes users more interested and increases the number of sales.
Customized features: Customized features on your website can make the user experience better and give your website unique features that make it stand out. Your local developer can make custom features for your business, like interactive maps, online booking systems, and social media integrations.
Personalized content: Your local web developer can make the content of your website more relevant to your target audience by making it more personal. They can give personalised suggestions, blog posts, and videos that meet the needs and interests of individual users.
Customized analytics: Your local developer can provide customised analytics that help you to better understand user behaviour on your website. They can look at data to find places to improve and give personalized suggestions to make the user experience and engagement better.
Overall, customization and personalization are important parts of website maintenance that can help improve user experience and engagement. By working with a local developer, you can make a website that fits your brand, has unique features, and keeps your target audience interested.
Talking and being able to reach
Effective communication and accessibility are important parts of website maintenance that can help improve the user experience and make sure that your website meets the needs of all visitors. Here are some ways your local developer can help with communication and access:
Accessibility:
Your local developer can make sure that everyone, even those with disabilities, can use your website. They can add things like alt tags for images, keyboard navigation, and audio descriptions for videos so that everyone can use your website and navigate it.
Responsive design: If your website has a responsive design, it will work on all devices, like phones, tablets, and desktop computers. Your local developer can make sure that your website is optimised for all screen sizes, so that visitors can use it on any device.
Tools for communication:
Your local developer can give you communication tools like live chat, email forms, and social media integrations to make it easier for you and your website visitors to talk to each other. These tools can get your users more involved and help you get closer to your customers.
Support for multiple languages: If your business serves people from all over the world, offering support for multiple languages can help improve the user experience and get more people involved. Your local developer can offer multilingual support, such as translation services, to make sure that people from all over the world can use your website.
User testing:
Doing user testing can help you find ways to make your website more accessible and easier to understand. Your local developer can do user testing and give you personalised suggestions on how to improve your website’s user experience and communication.
Overall, good communication and accessibility are important for website maintenance because they make sure that everyone can use your site and interact with it. Your local developer can add accessibility features, responsive design, communication tools, support for multiple languages, and user testing to improve the user experience and make sure that your website meets the needs of all visitors.
Quick response time
Quick response time is an essential factor in website maintenance that can help to improve user experience and prevent potential problems from turning into major issues. Here’s how your local developer can help with quick response time:
Timely updates:
Your local developer can make sure that your website is regularly updated with the latest security patches, bug fixes, and feature enhancements. Updating your website at the right time can help you avoid problems and make sure it works well.
Regular maintenance:
Plugin updates, performance optimisation, and content management are all examples of regular maintenance that can help make sure your website runs smoothly and efficiently. Your local developer can do regular maintenance on your website to stop problems from happening and keep it up-to-date.
Monitoring and alerts: Your local developer can monitor and send you alerts to find problems before they get too big. They can set up automated tools to keep track of how well a website works and send alerts when there are problems that need to be fixed.
Support 24 hours a day, 7 days a week: Your local developer can help you with any problems at any time of day or night. This can help keep your website from going down and make sure that visitors can always get to it.
Proactive approach: Your local developer can take a proactive approach to website maintenance, making sure that any potential problems are fixed before they become big ones. This can help keep your website from going down and make sure it is always working at its best.
Overall, quick response time is an important part of website maintenance because it makes sure that any problems are dealt with quickly and effectively. Your local developer can make sure that your website is always running smoothly and efficiently by giving you timely updates, regular maintenance, monitoring and alerts, support 24 hours a day, 7 days a week, and a proactive approach.
Things to think about when picking a local developer
It’s important to find the right local developer for your website maintenance needs if you want to make sure your site works well. When choosing a local developer, here are some things to think about:
Expertise and experience: Look for a developer who has the knowledge and experience to maintain your website. Check their portfolio and reviews to make sure they have a history of maintaining websites well.
Communication and accessibility: Make sure that your local developer has good communication skills and is easy to reach. Look for a developer who is available to answer your questions and worries and who keeps you up-to-date on the maintenance of your website.
Services: Think about the specific services your local developer offers and make sure they meet your needs for website maintenance. Look for a developer who can do a variety of things, such as security updates, improving performance, managing content, and making the user experience better.
Cost and pricing model: Think about how much it will cost to maintain your website and how your local developer charges. Look for a developer whose prices are clear and who offers flexible pricing plans that fit your budget and the way you want to maintain your website.
Support and backup: Make sure your local developer offers support and backup services 24 hours a day, 7 days a week. This will make sure that your website is always online. Look for a developer who offers regular backups and disaster recovery services to make sure that your website’s data is safe and secure.
Reputation and references: Find out how well-known your local developer is and ask some of their past clients for references. This can help you figure out how knowledgeable they are, how long they’ve been in business, and how happy their customers are.
Overall, when choosing a local developer for website maintenance, you should look at their expertise and experience, ability to communicate and be reached, services offered, cost and pricing model, support and backup, reputation, and references. By choosing the right local developer, you can make sure that your website works well and gives your visitors a great experience.
Reputation and past work
When choosing a local developer for website maintenance, you should think about their reputation and how much experience they have. This is why:
Reputation:
A local developer’s reputation is based on how well they do their job and how happy their customers are. Look for a developer who has a good reputation for maintaining websites in a good way. Check reviews and testimonials from the developer’s past clients to find out how happy they were with their services. You can also ask other business owners or coworkers who have used website maintenance services for recommendations.
Experience:
When it comes to maintaining a website, experience is very important. An experienced local developer has the knowledge and skills to handle a wide range of website maintenance issues, such as security updates, performance optimisation, and content management. They can quickly find problems and fix them, making sure that your website works well and smoothly. An experienced developer can also give you useful tips and suggestions on how to improve the way your website works and how users interact with it.
It’s important to look at a local developer’s portfolio and track record when thinking about their reputation and experience. Check out their past work to see if they have maintained websites like yours before. If they have worked with other businesses in your niche, they may know more about the challenges and opportunities there.
If you choose a local developer with a good name and a lot of experience, you can feel confident that your website is in good hands. You can count on them to provide high-quality website maintenance services, make sure your website is up-to-date and working well, and give you helpful advice on how to improve your website’s performance and how users interact with it.
Skill set and knowledge of technology
When choosing a local developer for website maintenance, it’s important to think about their skillset and knowledge of technology. This is why:
Skillset: Maintaining a website takes a wide range of skills, such as knowledge of security, performance optimisation, content management, and user experience. When looking for a local developer, it’s important to make sure they have the skills to take care of all the different parts of website maintenance well. Look for a developer who has a lot of experience and skills in different areas of website maintenance. They should be able to quickly spot problems and come up with good solutions to make sure your website runs smoothly and efficiently.
Technology knowledge: The technology landscape is always changing, so it’s important to have a local developer who stays on top of the latest trends and technologies. They should know a lot about the tools used to build websites, like HTML, CSS, JavaScript, and PHP. They should also have worked with Content Management Systems (CMS) like WordPress, Joomla, Drupal, and Shopify. Also, they should know how to host websites and manage databases so that your website runs smoothly and without any problems.
When choosing a local developer, think about what skills they have and what they know about technology. Ask them what they know about different kinds of technology and how they keep up with the latest trends and developments. Check their portfolio and reviews to see if they have worked with similar technologies and platforms before. You can also ask for references to find out more about how good they are at maintaining websites and how long they have been doing it.
Having a local developer with a wide range of skills and knowledge of the latest technology can help your website stay competitive and work well. They can find problems and fix them quickly. They can also make sure that your website uses the latest technologies and give you useful tips on how to improve its performance and the user experience.
Pricing and packages
When choosing a local developer for website maintenance, it’s important to think about pricing and packages. This is why:
Pricing: The cost of website maintenance services can vary a lot depending on the developer’s experience, skill set, and the size of the job. Some developers charge by the hour, while others offer packages for a set price. It’s important to understand how the developer sets their prices and what services come with their package.
It’s important to find a balance between price and quality when setting prices. Even though it may be tempting to choose the cheapest option, a low-priced developer may not have the skills or experience to provide high-quality website maintenance services. On the other hand, if you only need basic maintenance services, a pricey developer may not be the best choice.
Packages: Depending on the level of service they offer, local developers may offer different maintenance packages. Some developers offer basic packages that include things like security updates, backups, and plugin updates, which are all important parts of keeping a website running. Other developers offer full packages with extra services like performance optimisation, content management, and improvements to the user experience.
When looking at packages, it’s important to pick one that fits your needs and your budget. Look for a developer who offers packages that can be changed to fit the needs of your website. A developer who offers different packages is also a good choice, since you can pick the one that fits your needs and budget.
When choosing a local developer for website maintenance, it’s important to think about how much they charge and what packages they offer. Look for a developer with clear pricing, packages you can change, and a good balance between price and quality. With the right price and package, you can get high-quality website maintenance services that keep your site up-to-date, secure, and running well.
Wrapping Up
In conclusion, regular website maintenance is important if you want your site to be up-to-date, safe, and work well. Common maintenance tasks include security updates, performance optimization, content management, user experience improvements, broken link and error checks, mobile responsiveness testing, backups, and disaster recovery.
We Fix, Host, & Maintain WordPress Websites
At mywebmaintenance.com we provide instant WordPress technical support. We also provide bespoke web hosting & expert management for thousands of WordPress websites. Use us for quick one-time fixes, or partner with us for ongoing WordPress website maintenance. Follow us on Facebook to find out where we are next.
The Importance of Regular Website Maintenance Read More »








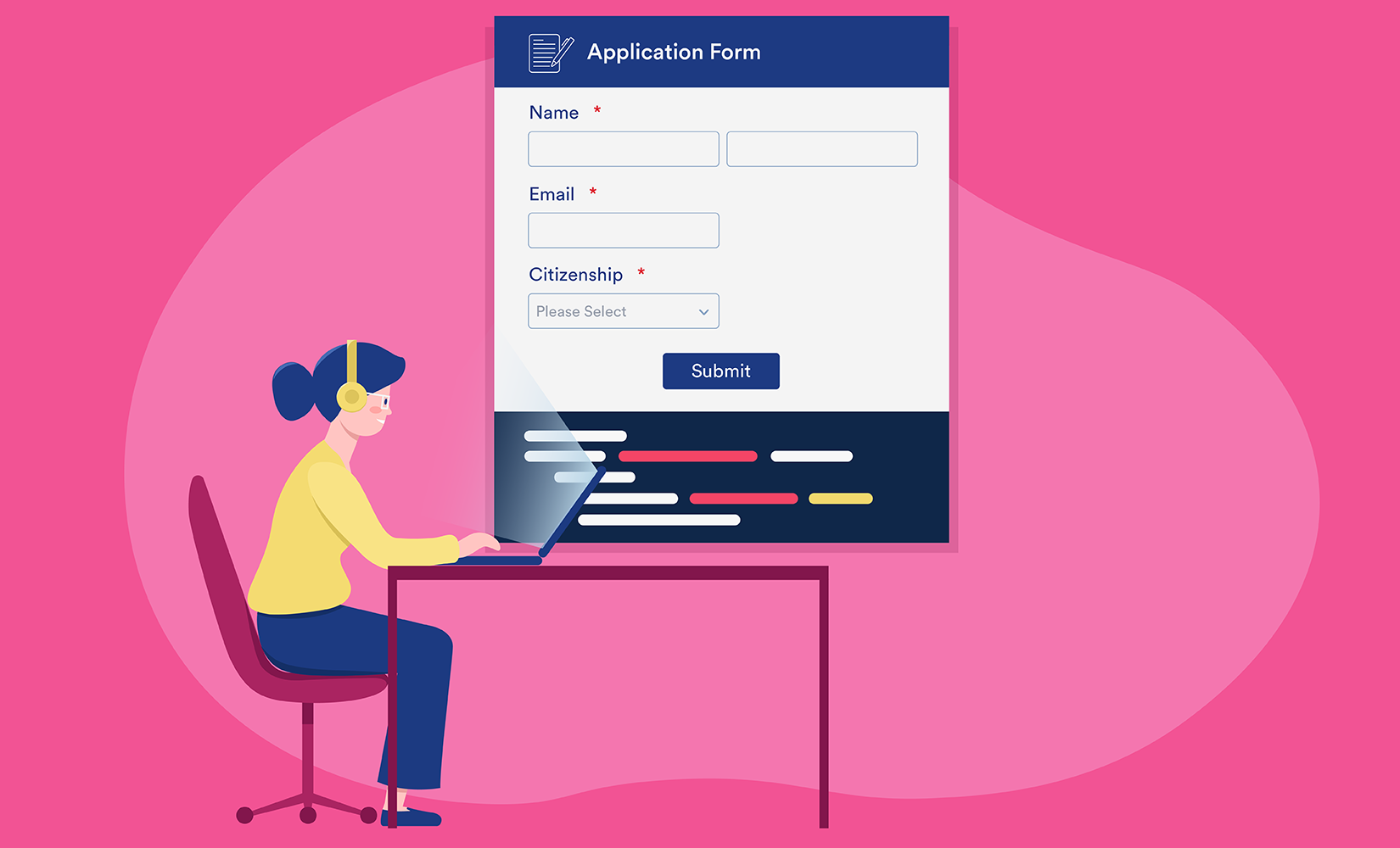 Contact forms are an essential part of any website, allowing users to communicate with the website owner or administrator.
Contact forms are an essential part of any website, allowing users to communicate with the website owner or administrator.








![Website Maintenance Checklist 2022 [Tasks+Cost+Importance]](https://www.globalmediainsight.com/blog/wp-content/uploads/2021/12/Website-Maintenance-Checklist.jpg)