Why Is Security Monitoring Important?
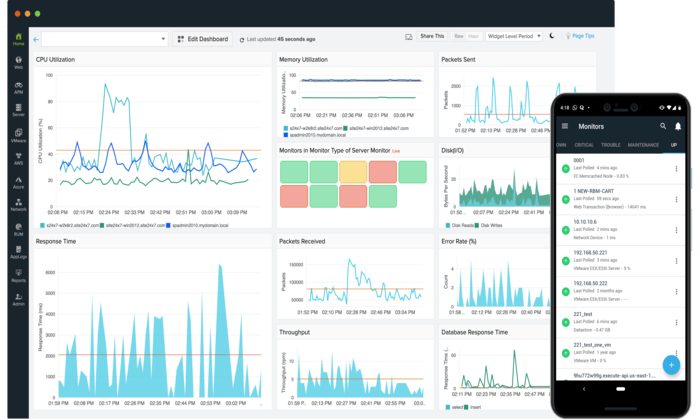
Knowing what’s taking place under the hood of your network and computer systems is incredibly important for your company’s security. It gives you critical insight into the threats you face and provides the information you need to quickly and efficiently resolve security issues as they arise.
A data breach can cause irreparable damage to your operations, finances, and reputation. Security monitoring can help you stay one step ahead of attackers.
What is security monitoring?
Security monitoring collects and analyzes information to detect unusual behavior or unauthorized activity on your network. That allows you to detect incidents early and respond to them more effectively.
With the visibility and understanding gained from collecting information from your network, security controls, servers/endpoints, and user applications, you can create a set of triggers that alert the business when something is wrong.
Not only can you set alerts for malicious behavior from outside your network, but you can also detect unusual activity by your employees, making it more difficult for attackers.
With cyber threats on the rise and tech-savvy, sophisticated criminal gangs on the rise, you must be able to spot incidents before they cause severe damage and take effective action quickly.
It is essential because cyber threats are on the rise. There are many kinds of security incidents – ransomware, social engineering (e.g., phishing), and hacking – but the question of who is behind the threats has taken cybersecurity to a new level. While there are still local threats and petty crimes, the threat from organized crime, state actors, and terrorist groups is growing. These attackers target financial and critical national information and are determined to cause widespread disruption if necessary.
The problem is that organizations typically don’t have the awareness or resources to realize they are under attack until they receive the ransom demand or their data is published on the dark web. By frequently monitoring your systems, you have a better chance of limiting the damage in the early stages of an attack.
How does security monitoring work?
Security monitoring aims to enable your organization to detect attacks, malicious activity, incoming data security threats, or even lurking problems within your systems. Having all relevant data collected and part of the alert is critical to understanding the incident so the situation can be quickly diagnosed and remediated. That is achieved by looking for patterns in the data, either from a single source, such as a user system, or by correlating it across multiple systems and sources to create a picture of an incident that the security team can investigate.
Attackers can linger on your network for weeks and months, waiting for an opportunity to strike. It takes approximately 280 days to detect and contain a vulnerability, so you must manage your defenses and respond quickly. Piers Wilson, head of product at Huntsman protection, states, “Speed is important. The time it requires to detect and respond to an attack makes a big difference in terms of the damage it does, the amount of data stolen, and the impact on the business’s reputation. Time is of the essence!”
However, all of this puts a massive workload on the team that has to deal with all of these alerts. Without centralized oversight and agreement with the business on what constitutes a significant risk, this job can be overwhelming, specifically if you have a small IT group.
Threats evolve daily, and many escape detection. New technologies leveraging AI can detect behavior patterns rather than just relying on information about previous intrusions to detect incidents. The tools learn over time and can process large amounts of data. The ability to detect the unusual in your systems increases the chances of protecting your business.
What is the distinction between security monitoring and SIEM?
The fact that your company has not suffered a security breach does not mean it has no vulnerabilities. A SIEM tool can be part of your security monitoring. SIEM is short for security details and event management. It combines two types of technologies: security information management, which is the analysis of data from your log files about threats and events, and security event management, which is real-time security monitoring that alerts you to important issues.
SIEM collects data from all types of devices, servers, domain controllers, etc., in your IT infrastructure and sorts them into categories such as successful and failed logins or malware activity. It correlates and analyzes this threat information across the IT environment to build a picture of past and current threats for effective detection and response. When it determines a threat, it generates an alert and defines the threat level of that alert so an organization’s security team can respond appropriately.
SIEM is just as good as the data it receives. However, SIEM often lacks context and the ability to distinguish between enterprise-approved and suspicious data activity. That’s why gathering data from both the enterprise and the cloud is essential to get the complete picture.
What’s the distinction between security monitoring and network monitoring?
Do you wish to monitor the health of your network or the security of your networks, such as data and integrity monitoring?
Network monitoring looks at the elements of the network infrastructure, while security monitoring includes file and integrity monitoring.
Network monitoring tells you how well your platform is, running-whether there are bottlenecks, errors, or devices offline. Some of these issues could be due to malware. In this case, security monitoring provides additional alerts and protection.
The benefits of network monitoring
1. Visibility of the network
You require to be able to monitor every element of your network. That includes all the devices connected to your network and the traffic that flows through it. It is the best way to keep an eye on the health of your network and identify performance issues.
Keeping track of all the tools on your network can be challenging. Automated network mapping tools can provide a complete view of even the most complex ecosystems as part of your network monitoring.
2. Maintaining compliance
Organizations that need to maintain regulatory compliance need the appropriate network monitoring tools. PCI DSS, HIPAA, FISMA, SOX, and others need network monitoring as part of the internal control structure for compliance, in addition to the external security controls already in place.
3. Preventing downtime
Downtime is a productivity killer and very expensive. In a recent survey, 40% of companies said an hour of downtime costs between $1 million and $5 million.
Monitoring can help you prevent unexpected downtime. An essential aspect of network monitoring solutions is detecting warning signs that could indicate a device failure or network problem. This way, you can identify the problem and prevent downtime.
Network monitoring helps prevent downtime and enables IT teams, to optimize performance to run operations more efficiently.
4. Find and fix problems quickly
When a problem occurs, network monitoring helps you isolate the problem faster. Whether it’s a traffic fluctuation, a configuration mistake, or something more serious, network maps can help you quickly find the source of the problem. Network automation tools that are part of your monitoring solution can fix many problems automatically.
Lowering the mean time to repair (MTTR) reduces downtime or poor network performance, and your IT team can concentrate on other issues.
5. Detect security threats
Network monitoring is primarily for performance monitoring, but it can also help uncover security threats in your system. Malware or viruses may not be visible at first glance, but your network monitoring solution can highlight unusual activity, such as suspicious use of network resources. You can detect small threats by continuously monitoring for unusual or suspicious activity before they become significant.
You can also proactively detect unauthorized access or security threats such as DDoS attacks or unauthorized downloads.
6. Bandwidth usage monitoring
If your bandwidth is overloaded, you’ll have unhappy employees and customers. By monitoring bandwidth usage, you can identify when slowdowns are occurring. When bandwidth usage reaches a critical level, you’ll be alerted so you can adjust your quality of service (QoS) protocols or take other steps to improve performance.
7. Capacity planning
User needs are also constantly evolving. As a result, it can be challenging to predict how and where users will use network resources in the future. As utilization increases, planning for additional infrastructure and capacity to meet this demand is essential.
By actively tracking and monitoring performance and utilization, you can use network-monitoring software to identify when utilization is skyrocketing. You can better anticipate future capacity and upgrade the network by comparing current performance.
Historical data can also help justify future investments when it comes to budget. Suppose you can provide evidence that the network is slowing down or performance is degrading due to increased utilization. In that case, convincing executives that you need to upgrade systems is much easier.
8. Deploy new technologies
Network monitoring is also essential when new technologies are to be deployed. It helps determine whether the network can handle additional resources and proactively identifies potential performance issues. After implementation, you can monitor the network to ensure performance doesn’t suffer.
9. Reducing the burden on IT teams
There’s also an underappreciated benefit of network monitoring tools. IT groups have a lot on their plate these days. Network growth and complexity have placed a significant burden on teams, which are typically understaffed and still expected to ensure perfect performance. The right network monitoring tools, like WhatsUp Gold, can significantly reduce this burden.
IT groups regain control of their network without manually addressing performance, receive proactive alerts when something is wrong, and reduce downtime. When an issue is detected, network monitoring solutions make it easier to identify, isolate and fix the issue.
That frees up time for team members to focus on other projects that can drive revenue growth. That can be invaluable.
10. Return on investment
Network monitoring also offers a measurable ROI. If you save one hr of downtime annually, monitoring has more than paid for itself. Add in the reduction in support calls, time spent troubleshooting issues, and maintaining the network performance needed to be efficient, and you can see how quickly the ROI adds up.
Why is continuous monitoring so important?
By monitoring the behavior of your systems 24 hours a day, seven days a week, 365 days a year, you shorten the time between detecting a threat and taking action. Consistent snapshots of real-time activity give you one of the best ways to detect a malicious user.
Around-the-clock monitoring also helps you identify the vulnerabilities and strengths of your IT infrastructure, providing valuable business insights that help you develop a sustainable and effective risk management strategy.
How does security monitoring help with compliance?
The National Cyber Security Centre alerts that a failure to monitor systems can result in attacks going unnoticed, which in turn can result in your failure to comply with legal or regulatory requirements. It recommends that organizations comprehensively understand how users access systems, services, and information.
Security monitoring helps measure or verify compliance. If you don’t have a record of activity related to the security controls, you won’t be able to demonstrate compliance – a common compliance failure.
Protecting your data and systems
Security monitoring helps detect sophisticated threats that can bypass traditional security tools. It can find a broader range of threats and reduces the time it takes to defend against attacks.
Compliance is critical, but it is the “floor,” not the “ceiling.” The objective of protecting data and systems – keeping private data private – is the very purpose of security monitoring. It provides information on which the company can act.
Setting up a security operations center is expensive. It can be time-consuming for your security team to sift through all the automatically generated alerts, risking missing a critical security event. The alternative is to utilize a managed service from a trusted third-party provider.
The Security Standards Organization (CREST) notes that “organizations of all types struggle to identify and effectively address potential cybersecurity incident indicators.” The organization recommends that organizations engage the services of one or more specialized third-party vendors for all or part of their security activities.
Whatever you decide, when the worst happens, around-the-clock security monitoring gives you the information you need to make quick decisions and analyze events.
At mywebmaintenance.com we provide instant WordPress technical support. We also provide bespoke web hosting & expert management for thousands of WordPress websites. Use us for quick one-time fixes, or partner with us for ongoing WordPress website maintenance.
Enjoy the post? For more posts, please visit My Web Maintenance
Why Is Security Monitoring Important? Read More »